Blog post
How Fraudsters Are Stealing Unemployment Insurance Money
Max Blumenfeld, Co-Founder, COO and Head of R&D
Published
June 3, 2021
Hundreds of billions of dollars issued in unemployment insurance
In the wake of the COVID-19 pandemic, Congress passed two economic stimulus packages worth approximately $4T; the Cares Act and American Rescue Plan Act.
Each provided enhanced and expanded unemployment insurance to millions of workers throughout the country.
Between March 2020 and March 2021, over $600B has been paid out in unemployment insurance benefits to over 40M Americans. Unfortunately, a significant amount of that money went to fraudsters. The U.S. Labor Department's Office of Inspector General estimates that $89B was issued to fraudsters, and there are some estimates that the number may be significantly higher than that.
Stolen credentials used to obtain unemployment insurance funds
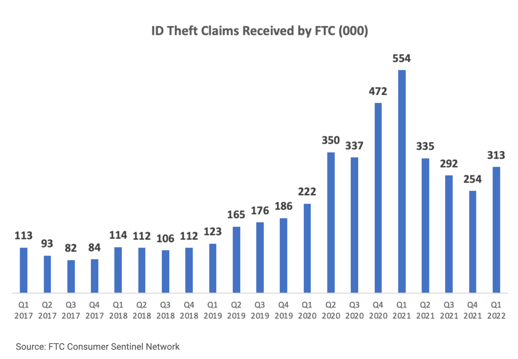
Most would agree that stolen credentials are being used to obtain these unemployment benefits funds. The data from the Federal Trade Commission would support this. Below is a chart that shows the ID theft claims received by the FTC. In 2020, the number more than doubled compared to 2019 (1.38M vs. 651K) and then stayed elevated in 2021 at 1.43M. As of Q1 2022, the number of ID Theft claims is still high relative to pre-pandemic times at 313K vs. 123K in Q1 of 2019.
How exactly are fraud rings, rappers, and one-off fraudsters using stolen credentials to steal unemployment benefits?
The scam to steal unemployment insurance benefits
Stolen credentials used to open a deposit account
The scam is simple - a fraudster uses stolen credentials to open a deposit account using the name, date of birth, Social Security number, and address of their victim. Then, the fraudster creates an unemployment insurance online account using these same stolen credentials. In California, for instance, this entails supplying a name, date of birth, Social Security number, and EDD Account Number which can be generated here.
The reason these fraudulent deposit account applications often get approved is because the address provided matches that of the victim. Typically, the financial institution will use a name, address, SSN, DOB match as sufficient grounds for approval.
Once a deposit account is opened, and the unemployment benefits have been processed, the fraudster remits the funds to the fraudulently opened deposit account. When the funds are received, they can be laundered through a myriad of other financial accounts such as other deposit accounts, peer-to-peer payment services or cryptocurrency platforms.
The ability to transfer funds into and out of a deposit account is generally available within three days of an account being opened. Unfortunately, when a deposit account is opened, the account owner only receives a debit card or welcome kit seven to ten days after the account was opened in the mail. At this point, the funds have typically been received into the fraudulent account and moved to a new account.
Some fraudsters will ask for their unemployment benefits to be issued to a debit card, rather than transferred to a deposit account via ACH. In these cases, they typically list an address on their unemployment insurance application that they control, rather than the address of the victim.
The byproduct of all of this is a massive influx of fraudulent applications to banks, credit unions, fintechs, or any institution offering a deposit account. Fraudulent applications could make up as much as 30% of all incoming deposit account applications or membership accounts applications in the case of credit unions.
Money mules used for the deposit account
A similar version of this scam involves the use of money mules - someone who (often unknowingly) illegally moves money on behalf of someone else. Instead of using stolen credentials to open a deposit account, fraudsters will sometimes convince someone with an existing deposit account to accept fraudulent money into their account. The fraudster then convinces the money mule to withdraw the money and give it to them either directly or through other anonymous means like Bitcoin; or to move the money electronically to other accounts managed by the fraudsters. Romance scams are a popular ploy to recruit money mules.
How to catch this scam
Strong identity verification controls are required to catch this scam when stolen credentials are used to open the deposit account. Verifying things like phone, email and identity velocity are example indicators that may signal the use of stolen credentials. Only when fraudulent deposit account applications are flagged as high risk can financial institutions conduct the appropriate review to check for fraud and reject if appropriate.
When money mules are involved, detecting this scam requires verifying the name of the unemployment insurance beneficiary matches the name on the deposit account. The challenge is in knowing when to perform this manual or automated verification. Some financial institutions set up transaction monitoring to flag accounts where the government benefit is issued from a state that is different than the state listed on the deposit account.
The key to mitigating this money laundering risk is flagging the fraudulent deposit account applications as high risk or the incoming benefits as suspicious. If they go unnoticed, the illegitimate money will likely be laundered through the financial system.
For more information on what we are seeing and how we can help, you can reach us here.
________________________________________

Max Blumenfeld is Co-founder and COO of SentiLink. Prior to SentiLink, Max led Risk Operations and Fraud Data Science at Affirm. Max holds a degree in mathematics and economics from the University of Chicago and was named to Forbes’ 30 Under 30 list in 2020.
Related Content
Blog article
April 3, 2024
Tips from a Fraud Fighter for Spotting Assumed Identity Abuse
Read article
Blog article
February 29, 2024
Reducing Complexity in Model Risk Management with Attributes
Read article
Blog article
January 18, 2024